Today marks a milestone for me. I started a blog. I have no idea how long I’ll write this, but something I found out recently compelled me to share what I know. I was completely and totally shocked at what I found and the implications of this security hole, in my opinion, are staggering. I felt so compelled that I paid for a SquareSpace site and wrote this entry.
Introduction
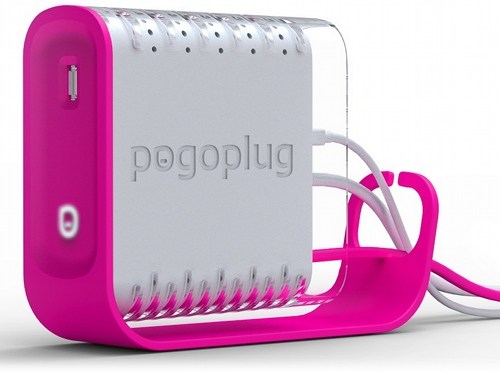
If you’ve been living under a rock, or just don’t frequent technology blogs and technology podcasts, then I suppose it’s possible you’ve never heard of a PogoPlug. A PogoPlug is a small device (really small in Version 1, and medium small in Version 2) that connects to your Internet network via Ethernet and then connects to stray USB drives you have laying around. It then has the ability to make the content of those USB drives available both on your local network as Network Attached Storage (NAS) and, more importantly, available via the Internet on a web site controlled entirely by you. I, like many others, believed this was a great way to take USB drives I have laying around doing nothing, and convert them into useful storage for my local network as well as provide a way to share files with people elsewhere on the Internet.
I was wrong.
Bad
The PogoPlug has open SSH access to the root account.
Badder
The password is published on the Internet, by CloudEngines, and is easy to find with a Google search. Just Google: PogoPlug SSH linux. It’ll be your first hit. But, to save the time, I’m posting the direct URL here: http://www.cloudengines.com/dev/linux.html
In case they were to take the page down, here is an image of the site:
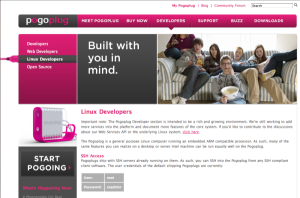 Well Known Password Exposed
Well Known Password Exposed
Worse
You cannot change this password without crippling CloudEngines’ ability to upgrade your device. Now pause for a moment. Yes, that means that in order to upgrade your device, they are most likely SSHing into your PogoPlug, as root, and running upgrade scripts. Yay! For what it’s worth, here are the instructions, that I got from CloudEngines, to change your root password on the PogoPlug. Bear in mind, you will no longer get updates and will not be able to upgrade it until you’ve set the password back to the default
Login to the PogoPlug via SSH as root, then:
# passwd
— new password at prompt
# mount / -o remount,ro
Worst
If you opt not to change the password, then know that your PogoPlug is potentially wide open to anyone who knows this well published username and password. Once they SSH into your PogoPlug, they have ACCESS TO ALL OF YOUR DATA. It doesn’t matter what permissions you’ve set via the web interface, they have root access to your device and they can see everything that is connected to it AND COPY IT OFF.
Conclusion
I’ve read lots and lots of positive comments about the PogoPlug, how easy it is to get working (despite my personal experience) and how great the overall device is for managing storage and making it available over the Internet. However, that ease of use has a serious price, and that price is too high for me to use it. I’ve sent mine back and CloudEngines was nice enough to provide me an RMA.